Lazarus attempt to launder additional $27.2M of funds stolen from Harmony bridge hack
On-chain analysis shows that North Korean hackers responsible for Harmony’s Horizon bridge hack spent the weekend attempting to move some of the illicit funds.
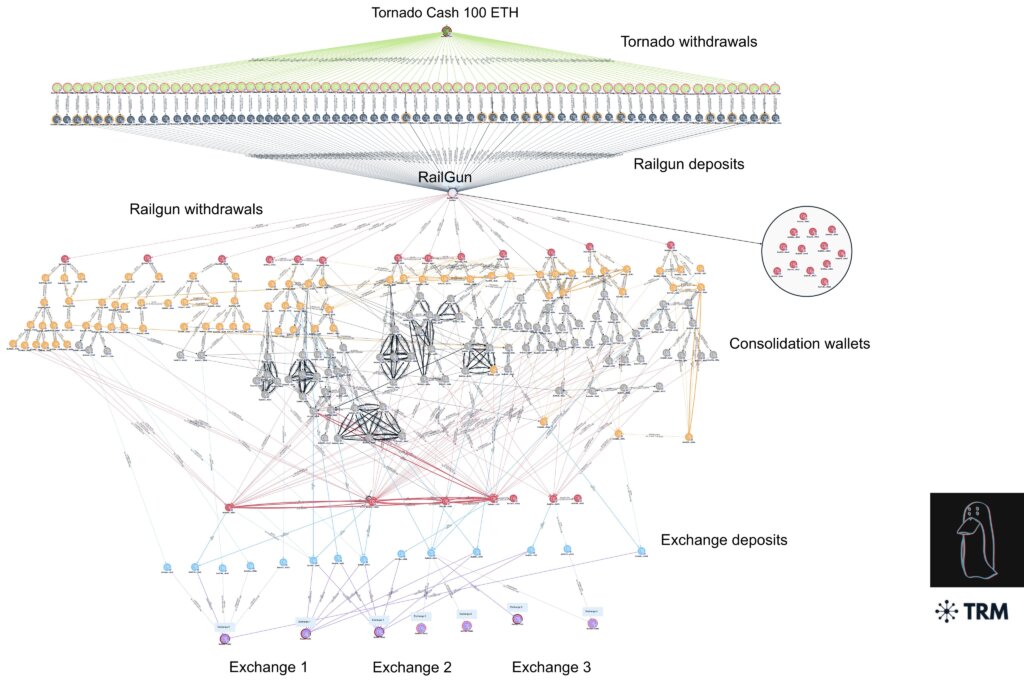
Using Railgun, a smart contract system that initiates what is known as “Zero Knowledge Proof,” the hackers attempted to move the illicit funds through six different exchanges, several of which were notified over the weekend.
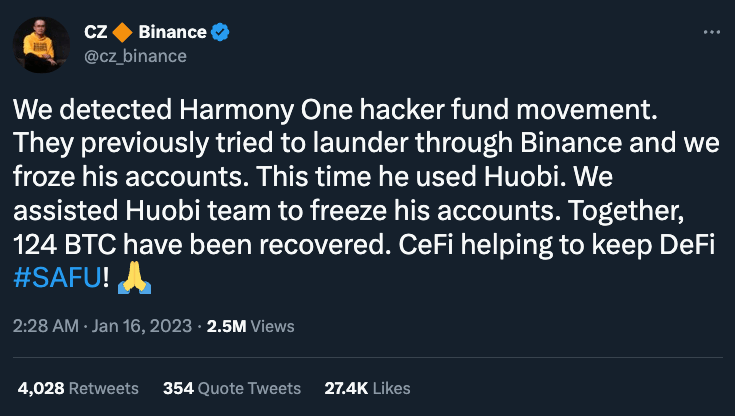
At least two of the exchanges, Binance and Huobi, were able to move fast and freeze at least a portion of the laundered funds.
The movements come more than a week after the FBI declared Lazarus group, which has links to the Democratic People’s Republic of North Korea (DPRK), as responsible for the exploit of Harmony’s Horizon Protocol, which saw in total more than $100 million worth of cryptocurrency disappear in an attack in June 2022.
That attack and others like it, the FBI allege, are spurring “the DPRK’s use of illicit activities—including cybercrime and virtual currency theft—to generate revenue for the regime.”
Since 2017, $1.2 billion worth of crypto has been stolen by the group, according to an Associated Press report.
The largest of which was the $624 million hack last April of the Ronin Network, Axie Infinity’s side-chain link to the Ethereum network.
Since the proliferation of decentralized finance, or DeFi, bridge attacks are becoming increasingly more common.
What are the common types of bridge exploits?
The exploitation of bridges in the world of blockchain is often sophisticated and predictable due to code bugs or leaked cryptographic keys. Some of the most common bridge exploits include:
- False Deposits: In this scenario, a bad actor creates a fake deposit event without actually depositing funds or uses a valueless token to infiltrate a network, such as that which occurred in the Qubit finance hack last January.
- Validator Flaws: Bridges validate deposits before allowing transfers. Hackers may exploit a flaw in the validation process by creating fake deposits, which occurred during the Wormhole hack where a flaw in digital signature validation was exploited.
- Validator Takeover: Here attackers seek a vulnerability by attempting to gain control over a majority of validators by taking over a certain number of votes to approve new transfers. The Ronin Network hack is an example where five of the nine validators were compromised.
It is important to note, however, that the most common factor across exploits is human error. Instead of focusing solely on the shortcomings of bridges, post-hack investigations are usually able to patch security fixes, but only after the damage has already been done.
The sheer magnitude of these exploits is concerning for blockchain developers. Other notable bridge exploits from 2022 include:
- February: Wormhole — $375 million
- March: Ronin Bridge — $624 million
- August: Nomad Bridge — $190 million
- September: Wintermute — $160 million
Credit: Source link


Comments are closed.